FORUM CTRLX AUTOMATION
ctrlX World Partner Apps for ctrlX AUTOMATION
Dear Community User! We are updating our platform to a new
system.
Read more: Important
information on the platform change.
- ctrlX AUTOMATION Community
- Forum ctrlX AUTOMATION
- Communication
- Re: Guide for using ctrlX core as a "router" with firewall app and VPN client
Guide for using ctrlX core as a "router" with firewall app and VPN client
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-18-2022 02:01 PM
Is there a guide for using ctrlX core as a "router" with firewall app and VPN client available?
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-10-2021
07:31 PM
- last edited on
05-18-2022
02:03 PM
by
CodeShepherd
![]()
Hi to everyone,
This is not a question but is actually a sort of guide created from the experiences that me and @TheCodeCaptain have collected about the topic together.
"Disclamer: this procedure is not addressed to the basic user, in order to fully understand what is happening and to debug the setup it is necessary a good knowledge about IPtables, networking and VPNs. Furtermore the guide is not a complete setup to a production case, is just a proof of concept that, the user, must be able to develop in order to fit his own case"
Experience1:
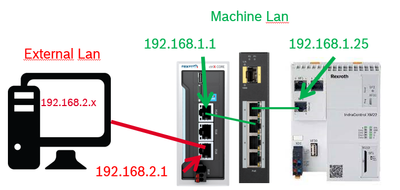
Objective: we would like to login inside the XM22 passing trough the ctrlX core. Just like the picture below.
The test has been done with:
- ctrlX core release 21.11 eth0: 192.168.1.1, eth2:192.168.2.1
- App Firewall 1.12.0
Step1: Get the possibility to forward packets.
In order to forward packets it is necessary to allow it from the eht0-1 interfaces:
From firewall point of view it is also necessary to allow the packet forwarding (by default it is allowed).
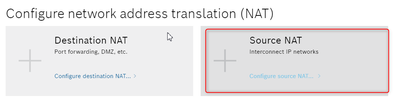
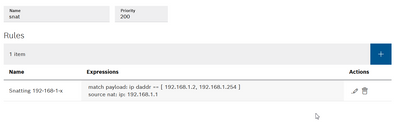
Step2: SNAT
Now it should be possible to connect to the PLC but it is necessary to set up the XM22 Gateway: it must be the ctrlX core IP address, in this case being the xm address 192.168.1.25 it must be 192.168.1.1. Otherwise the connection wouldbe dropped by the PLC.
In order to avoid this configuration for the PLC or the others devices on the machine network it is possible to setup a simple SNAT routing rule. Assuming again tath the ctrlX core address from the machine point of view is 192.168.1.1 here is my configuration adopted.
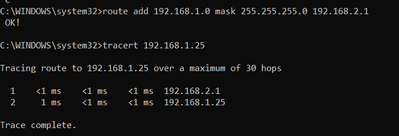
Step3: PC routing
Now that anything has been set up in ctrlX it is necessary to setup the right rules also inside the PC.Being the PC address 192.168.2.X and the ctrlX coro eth1 address = 192.168.2.1 the rule to be entered is the following:
route add 192.168.1.0 mask 255.255.255.0 192.168.2.1
It means that we're trying to reach a 192.168.1.X address passing trough 192.168.2.1 which is the ctrlX core.it It is possible to check the connection using the command "tracert".
The Experience with the VPN will follow.
Mauro